Download
Security_Operations_7.4_Analyst_Exam_Description.pdf
Question :36
Refer to the exhibits.
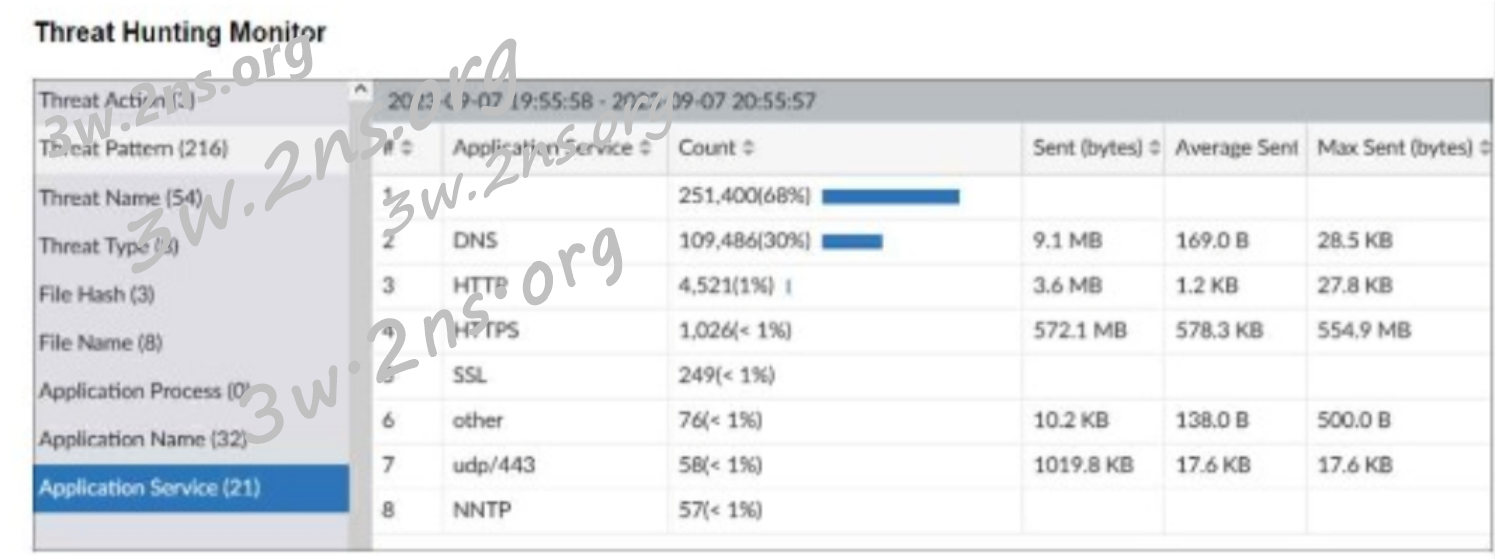
What can you conclude from analyzing the data using the threat hunting module?
A. Spearphishing is being used to elicit sensitive information.
B. DNS tunneling is being used to extract confidential data from the local network.
C. Reconnaissance is being used to gather victim identity information from the mail server.
D. FTP is being used as command-and-control (C&C) technique to mine for data.
Ans:B
[ add comment ] | permalink | print article | related link |




 ( 2.9 / 73 )
( 2.9 / 73 )

 Random Entry
Random Entry